Master of Science in Information Systems (MSIS) Computer Forensic Management
PROGRAM AT A GLANCE
12 master's courses
11 weeks long
$ 2540
Cost per course
Flexible learning
Online and in-person programs at select campuses, subject to availability
Why earn a degree in computer forensic management from Strayer?
Cyber forensics professionals help spearhead the critical work that drives the discovery, investigation and solution of digital theft, sabotage and even terrorism. The computer forensic management concentration of our online MS in Information Systems program puts you on the front lines of the battle for data security, privacy and protection.
Spearhead digital criminal investigations
Discover how forensic experts identify, track and catch cybercriminals. Strayer’s Computer Forensic Management program examines the latest cyber investigation methods, cybersecurity tools for catching dangerous hackers and how to manage digital crime scenes.
Skills you’ll learn with a Strayer MSIS, Computer Forensic Management concentration
A Strayer degree can help prepare you for career opportunities in computer forensic management while offering support, flexible learning options and career planning every step of the way.
- Understand and apply the control objectives for information and related technology framework to perform IT audits.
- Describe information technology general controls based on the Information Technology Infrastructure Library best practices.
- Identify the computer investigation process.
- Compare the various types of cybersecurity tools.
- Demonstrate the ability to develop procedural techniques in crime and incident scenes.
Earn your degree from an accredited university
Strayer University is an accredited institution and a member of the Middle States Commission on Higher Education (MSCHE or the Commission) www.msche.org. Strayer University’s accreditation status is Accreditation Reaffirmed. The Commission’s most recent action on the institution’s accreditation status on June 22, 2017 was to reaffirm accreditation. MSCHE is recognized by the U.S. Secretary of Education to conduct accreditation and pre-accreditation (candidate status) activities for institutions of higher education including distance, correspondence education, and direct assessment programs offered at those institutions. The Commission’s geographic area of accrediting activities is throughout the United States.

Master of Science in Information Systems (MSIS) in Computer Forensic Management cost breakdown
- 12 courses, $2540 per course
- $65 technology fee each term
- $150 one-time degree conferral fee
- $100 resource kit per course
Estimate the cost of your degree
How much does a Master of Science in Information Systems (MSIS) in Computer Forensic Management cost?
Estimate the cost of your degree
How much does a Master of Science in Information Systems (MSIS) in Computer Forensic Management cost?
Expected Graduation
...
Approximate Total
...
*Student is required to take two courses per quarter during disbursement period
PREPARING YOUR RESULTS
Time commitment
Calculate the approximate time commitment of your degree.
| Course load | ... courses/term |
| Classroom time | ... hours/week |
| Terms per year | ... terms |
| Terms to graduation | ... terms |
Cost analysis
Calculate the approximate cost of your degree
| Tuition | ... |
| Books | ... |
| Fees | ... |
| No-cost gen ed | $0 |
| Transfer credits | ... |
| Transfer Credit Scholarship | $0 |
| $4K scholarship | $0 |
| Strayer Learn and Earn Scholarship | $0 |
| Approximate total | ... |
Ways to reduce tuition
$4K Alumni Master’s Scholarship
If you’re a Strayer University Alumni and ready to pursue a master’s degree, our Alumni Scholarship can save you $4,000. All you need to do is register for an eligible Strayer graduate program, maintain a GPA of 2.5 or greater and meet eligibility requirements.
50% off Master’s Scholarship
Enroll in two master’s courses, get 50% off tuition.
*Eligibility rules, restrictions and exclusions apply.
Civic and Community Alliance Scholarship
Ready to earn an affordable Strayer degree? Admitted Strayer or JWMI students who are employed in certain civic roles or volunteer for a nonprofit may be eligible to receive 25% off tuition for the duration of their program.
Explore courses in Strayer’s Master of Science in Information Systems, Computer Forensic Management
From phishing schemes to ransomware attacks and data breaches, cybercrimes are constantly evolving – and so are the tools to fight it. Strayer’s curriculum equips you with the advanced forensic skills to investigate digital crimes and defend an organization’s most critical assets. You’ll learn how to collect, analyze and preserve digital evidence as well as report findings. The program examines frameworks for auditing and securing IT environments. Gain a deeper understanding of the technical and legal complexities of cyber operations and develop the skills to make ethical and informed decisions in the field of computer forensics.
Computer Forensic Management Concentration Courses
Complete your degree from where you live, on your time, in a flexible, 100% online program. Using our online portal, you’ll be able to:
- Access lectures and coursework
- Complete assignments and exams
- Communicate with professors and classmates
- Access student resources and support
From day one, you’ll have a team of advisors and coaches to help you balance college, work and your personal life. Tap into support resources online or at a campus near you.
You’ll have access to:
- Admissions and enrollment support
- One-on-one academic coaches
- Financial guidance and potential cost savings
- Career planning services
The faculty at Strayer University bring years of real-world industry experience to the classroom, offering valuable insight and practical knowledge. They are committed to supporting your professional goals and are responsive to questions and concerns through the virtual courseroom.
What can you do with an MSIS, Computer Forensic Management degree?
Your education can help you pursue your professional and personal goals. While Strayer cannot guarantee that a graduate will secure any specific career outcome, such as a job title, promotion or salary increase, we encourage you to explore the potential impact you can have in the information systems field.
Versatile skills for your future
The computer forensic management concentration can provide the skills to help you identify, track and catch cybercriminals.
In addition, students who complete this concentration will be prepared to:
- Ensure digital media complies with legal policies and procedures.
- Produce system images or capture network settings from IT environments to keep as evidence.
- Create investigation strategies for computer crimes, violations or suspicious activities.
- Support cyber incident responses by maintaining cybersecurity software and hardware.
- Stay informed on laws, regulations, policies and other directives related to digital forensics or information privacy.
- Keep and safeguard digital forensic evidence for analysis.
- Monitor computer virus reports and decide when your organization should update its virus protection systems.
- Update computer security files to include new software, fix errors or modify individual access status.
- Record policies, procedures and tests for computer security and emergency measures.
- Manage data file use and control access to computer files to protect of information.
- Raise awareness about security and train users to help improve system security and server and network efficiency.
86
of Strayer master's alumni agree that Strayer was the right choice for earning their degree.
Strayer Alumni Survey, 2023
Apply for your Computer Forensic Management degree today
An admissions officer can help you choose the right program, register for classes, transfer credits and find cost-savings opportunities.
Here’s what you’ll need to get started:
Summer classes start on July 6
Learn more about Strayer University’s admissions process.
Transferring to Strayer from another university?
Transfer up to four eligible classes from a prior college or university to your master’s degree, saving time and money.
Strayer welcomes international students
Strayer University is proud to have hosted more than 4,000 international students from over 143 countries. Earn your degree in the U.S. or completely online in your home country – it’s your choice.

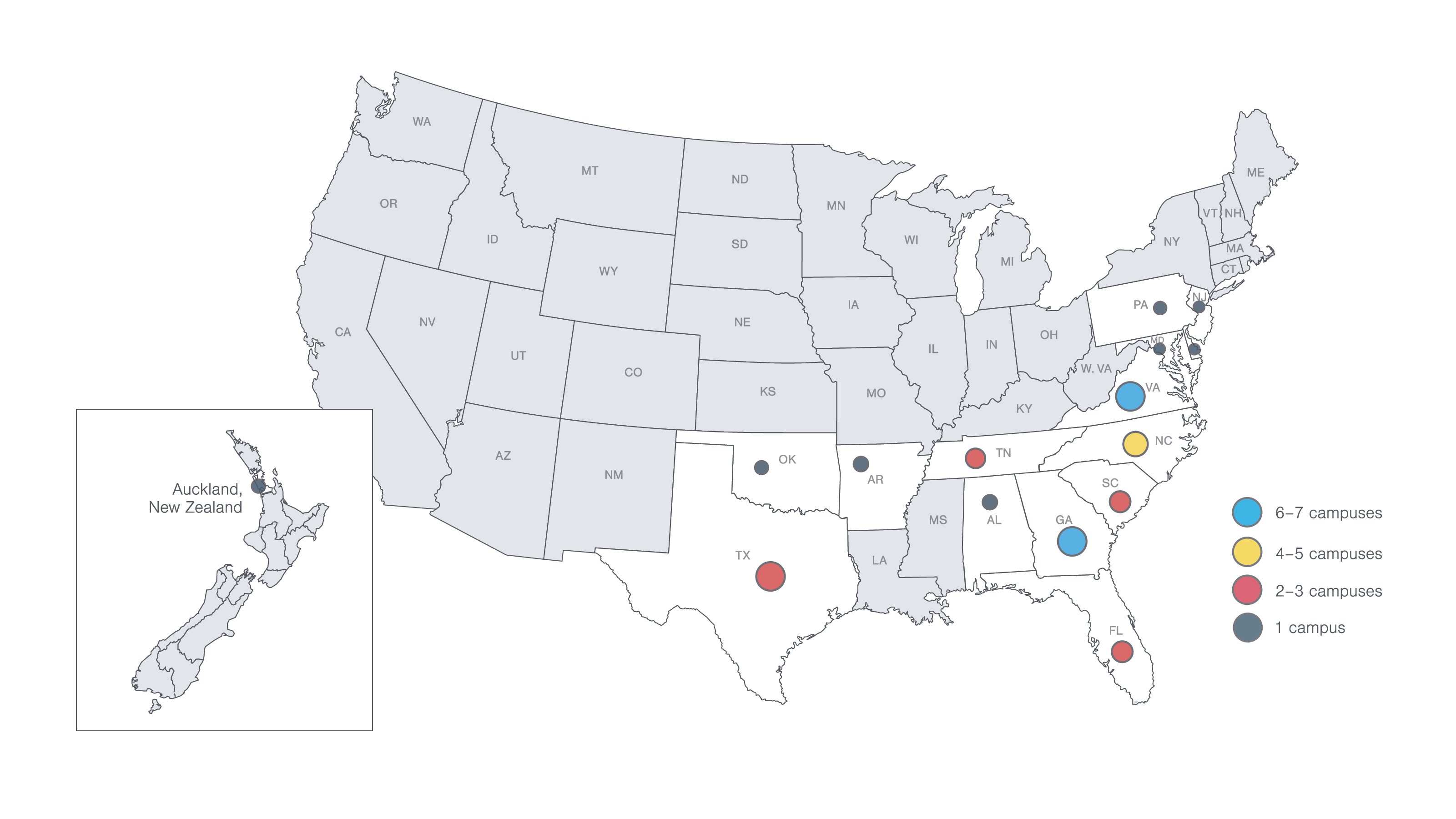
Campus locations
Come to a campus near you for guidance and support. You’ll have access to helpful resources, a supportive community and plenty of spaces to learn and grow.
Ready to take the next step?
Your admissions officer is here to guide you through every step of the process, from completing your application to choosing your concentration.